Security
Provides an overview of the Data Fabric security features.
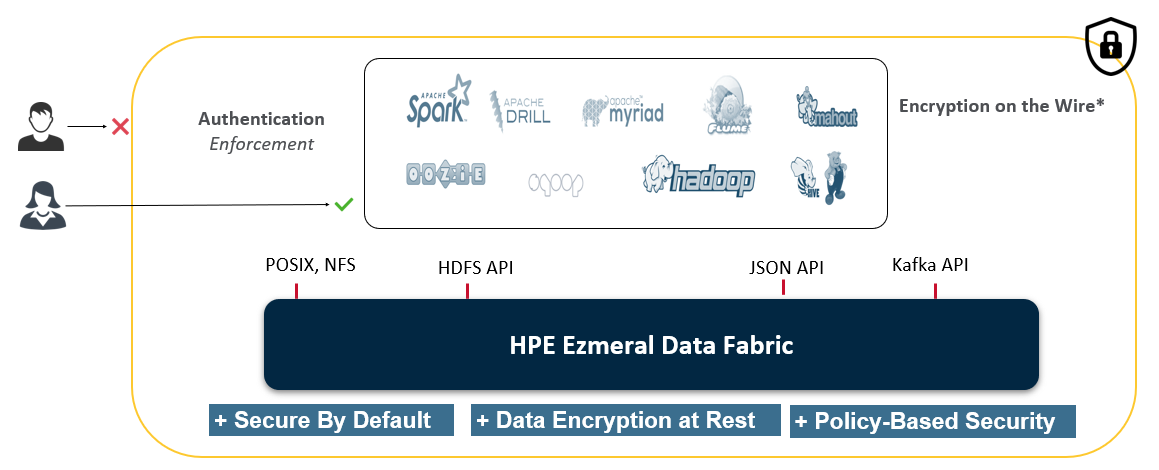
Securing enterprise data is critical. To make securing data in clusters easy, the HPE Ezmeral Data Fabric has a data protection scheme built directly into the platform that is enabled by default, simplifying the process of protecting critical data. You can take advantage of the default security settings, or you can implement data security manually. Either way, it is important to identify which data to secure.
Since data must be shared between nodes on the cluster, data transmissions between nodes, and from the cluster to the client are vulnerable to interception. Networked computers are also vulnerable to attacks where an intruder successfully pretends to be another authorized user and then acts improperly as that user. Additionally, networked machines share the security vulnerabilities of a single node. The HPE Ezmeral Data Fabric supports the ability to apply protection directly as data enters and exits the platform. You do not need to apply an external management server or particular security plugin.
- Secure by Default
-
Data Fabric, which includes the HPE Ezmeral Data Fabric and EEP components, is secure out-of-the-box on all new installations, ensuring all network connections require authentication and all data in motion is protected with wire-level encryption. Data Fabric provides the ability to apply security protection directly for data as it comes into and out of the platform without requiring an external security manager server or a particular security plugin for each ecosystem component. The security semantics are applied automatically on data being retrieved or stored by any ecosystem component, application, or users.
- Platform-Based Security
-
The HPE Ezmeral Data Fabric applies security semantics automatically as data is being stored and retrieved from the platform. It supports all four pillars of security (authentication, authorization, auditing, and encryption), using platform-level capabilities that do not require external security tools or plugins.
Starting with Data Fabric 6.2, the platform introduces support for Policy-Based Security. Policy-based security enables you to more easily manage the four pillars of security.
- Encryption
- On the HPE Ezmeral Data Fabric, data is protected by encrypting all data being transmitted over the wire and encrypting all data that is stored in the platform.
The following sections describe the Data Fabric security capabilities and security architecture.
Security Capabilities
A secure Data Fabric environment is predicated on authentication, authorization, auditing, and encryption capabilities. You can use policy-based security to classify and manage these capabilities.
- Authentication
-
Restricting access to a specified set of users.
Robust authentication prevents third parties from representing themselves as legitimate users. Data Fabric supports a wide range of authentication mechanisms depending on the network transport. These mechanisms include Data Fabric tickets, Kerberos, Pluggable Access Module (PAM), Basic Authentication, Data Fabric SASL, and SPNEGO.
See Configuring Authentication for more information.
- Authorization
-
Restricting an authenticated user's capabilities on the system.
Data Fabric provides sophisticated authorization controls to ensure that users can perform only the activities for which they have permissions, such as data access, job submission, cluster administration, and more. These permissions can be granted by an administrator through the browser-based Control System management and monitoring interface, or by using the command-line utilities.
See Managing Access Controls for more information.
- Auditing
-
Logging audit records of operations.
Data Fabric allows you to log audit records of cluster-administration operations and operations on directories, files, and tables.
See Managing Auditing for more information.
- Encryption
-
Restricting an external party's ability to read data.
Encryption is used to avoid exposure to breaches, such as packet sniffing and theft of storage devices. In a secure Data Fabric cluster, data transmission between nodes, and between a Data Fabric cluster and ecosystem application is encrypted, preventing an attacker with access to that communication from gaining information about the contents of the transmission. Optionally, you can enable encryption for data at rest to prevent unauthorized users from accessing sensitive data, and protect against data theft through sector-level disk access.
Data is protected by encrypting all data being transmitted over the wire and optionally encrypting all that is stored on the Data Fabric platform. The Data Fabric data encryption scheme is built directly into the platform and is enabled by default.
See Managing Encryption for more information.
- Policy-Based Security
-
Create security policies and apply them to data objects to simplify the management of security controls on data.
Policy-Based Security is a feature that administrators can use to classify security controls into a manageable number of security policies instead of defining security controls on individual data objects. The security controls defined in a security policy identify which users are authorized to access and modify data objects, whether to audit data operations, and whether to protect data in motion with wire-level encryption. When you apply security policies on data objects, such as volumes, files, and tables, the HPE Ezmeral Data Fabric automatically enforces the security controls defined in the policies during data operations. In cases where data is not associated with a security policy, the system enforces the security controls directly defined on data objects.
See Policy-Based Security for more information.
Security Architecture
Data Fabric provides the following authentication and authorization functionality:
- File System Permissions
- For files and directories on the Data Fabric cluster, you can leverage standard Unix-style permissions to grant access to authorized users. Since file system is a POSIX-like file system, you can set user permissions as you would on any other Linux system. See Setting file system Permissions for more information.
- Cluster, Volume, and Job Queue Access Control Lists (ACLs)
- You can specify the actions that a given user can perform on each of these cluster elements. You can use access control lists (ACLs) to grant permissions for performing administrative tasks at both the cluster and the volume level. See Managing Access Control Lists for more information.
- Access Control Expressions for File System and Natively Stored HPE Ezmeral Data Fabric Database Tables
- ACEs control which files, directories, volumes, streams, and tables users or groups can access. ACEs are a powerful and flexible mechanism to grant permissions on structured and unstructured data. See Managing Access Control Expressions for more information.
- Impersonation for Centralized Control of Access to Resources
-
Impersonation, also known as identity assertion, is one user accessing data and submitting jobs on behalf of another user. See Managing Impersonation for more information.
What to do Next
The secure-by-default data platform provides security through a single option in the Installer or by running the configure.sh script with the
-secure option after a manual installation. You can enable security on
your cluster using the procedure described in the following topics:
- Using the Enable Secure Cluster Option if you are installing with the Installer.
- Enabling Security if you are Installing without the Installer.
After enabling security, optionally, you can perform the following tasks:
- Understand the security exceptions and take corrective action, where applicable.
- Configure authorization on the resources.
- Configure auditing on administration and resources.
- Configure security policies to manage security controls on data resources.
- Configure encryption for data at rest.
- If you have Hive installed, enable storage-based authorization for the Hive Metastore server.